[DigitalToday reporter Chi-gyu Hwang] "Many people worry that AI will become overwhelmingly advantageous for hackers. But reality is not that simple."
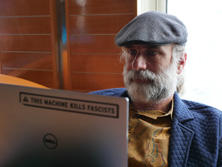
Bruce Schneier (브루스 슈나이어), a world-renowned cryptographer and security expert, examined the impact of Mithos, an AI model developed by Anthropic, on the cybersecurity landscape. He saw defence as likely to have the advantage over the long term in a contest between AI-powered attacks and AI-driven defence.
But he warned that for the next few years, persistent hacking incidents could continue until new standards take hold. Systems that are slow or impossible to update, such as cars, refrigerators and legacy financial systems, could face repeated hacks until solutions emerge.
He said there are areas that can respond relatively easily to threats from AI, and areas that cannot. Risks also vary by the type of vulnerability.
To that end, he classified vulnerabilities into 4 types.
The first type is vulnerabilities that can be automatically found, verified and even patched. The second type is vulnerabilities that are hard to find but can be quickly patched once discovered.
Cloud web applications built on standard software stacks are a representative example. Because updates can be deployed quickly, defence can sufficiently catch up, Schneier explained.
The third type is vulnerabilities that are easy to find but hard or impossible to patch. Examples include IoT home appliances and industrial equipment that are not well updated. The fourth type is vulnerabilities that are easy to spot in code but hard to verify in real environments. "In complex distributed systems where thousands of services run in parallel, it is difficult to distinguish real vulnerabilities from false positives," Schneier said.
Schneier stressed that distinguishing among the 4 vulnerabilities is the starting point for cybersecurity strategy in the AI era. That is because response methods do not completely change depending on patchability and the difficulty of verification. "In systems that update quickly, like smartphones, web browsers and major internet services, patches can be applied as quickly as AI finds vulnerabilities. Defence can catch up," he said.
The problem is systems that are hard to patch. "Systems that cannot be easily updated, such as refrigerators, cars, industrial control equipment and legacy financial systems, should be kept off direct internet connections and placed behind strict firewalls. The principle of least privilege, designing each component to have only the access it absolutely needs, is still valid," he said.
Schneier said software development practices also need to change in the AI era. "Using AI agents to repeatedly test attacks in real environments and filter out only real vulnerabilities, so-called VulnOps, will become a standard in the development process," he said.
He also expects documentation to become more important. "Just as developers need documentation to understand code, AI agents also refer to documentation when finding bugs. The better organised the documentation, the faster AI can grasp the code structure and the more accurately it can find vulnerabilities," he said. He added, "Using industry-standard tools and libraries rather than proprietary approaches matches patterns AI has already learned, allowing it to catch vulnerabilities better."
